Couldn't Read Packet: Connection Reset by Peer
Introduction
A remote machine has prevented an SSH connection you were attempting to plant or maintain. The "ssh_exchange_identification: read: Connection reset by peer" message is not specific enough to immediately explain what triggered the fault.
To be able to resolve the issue successfully, nosotros first need to identify its crusade. This article provides an in-depth analysis of the probable causes and provides the virtually effective solutions.
By reading this tutorial, you will learn how to set up the "ssh_exchange_identification: read: Connection reset by peer" Mistake.
Prerequisites
- Necessary permissions to access remote server
- A user account with root or sudo privileges
What Causes the "Connection reset by peer" SSH Error?
The "ssh_exchange_identification: read: Connectedness reset by peer" error indicates that the remote machine abruptly closed the Transition Control Protocol (TCP) stream. In most instances, a quick reboot of a remote server might solve a temporary outage or connectivity issue.
Note: Network-based firewalls or load-balancers can sometimes distort IPs or security permissions. This blazon of trouble can be resolved past contacting your service provider.
Learning how to troubleshoot this event, and determining the underlying cause, helps you prevent future occurrences on your organization. The most common causes of the "ssh_exchange_identification: read: Connection reset by peer" fault are:
- The connexion is being blocked due to the Host-Based Admission Control Lists.
- Intrusion prevention software is blocking your IP by updating firewall rules (Fail2ban, DenyHosts, etc.).
- Changes to the SSH daemon configuration file.
Check the hosts.deny and hosts.allow File
The hosts.deny and hosts.allow files are TCP wrappers. As a security characteristic, these files are used to limit which IP address or hostname can found a connection to the remote motorcar.
Notation: Inspect the hosts.deny and hosts.allow files on the remote server, not on the local customer.
How to Edit hosts.deny File
Access your remote server and open the hosts.deny file using your preferred text editor. If you are using nano on a Debian based system, enter the following command:
sudo nano /etc/hosts.deny Empty lines and lines starting with the '#' symbol are comments. Check if yous tin can locate your local IP or host-proper name in the file. If it is nowadays, it should be removed or commented out, or else information technology prevents you from establishing a remote connectedness.
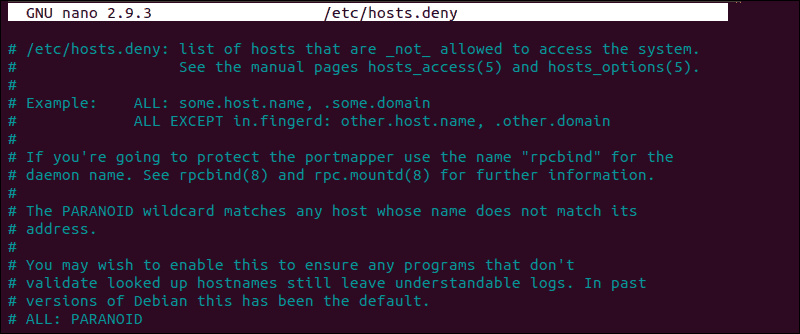
Later on making the necessary changes, salve the file and exit. Endeavour to reconnect via SSH.
How to Edit hosts.allow File
Every bit an additional precaution, edit the hosts.allow file. Access rules inside the hosts.allow are applied first. They take precedence over rules specified in hosts.deny file. Enter the following command to access the hosts.allow file:
sudo nano /etc/hosts.let Adding host-names and IPs to the file defines exceptions to the settings in the hosts.deny file.
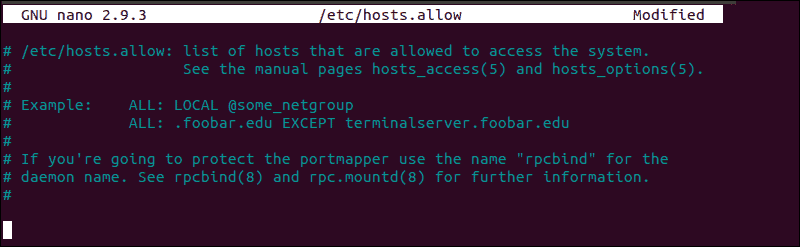
For example, a strict security policy inside the etc/hosts.deny file, would deny access to all hosts:
sshd : ALL ALL : ALL Later, you can add a single IP address, an IP range, or a hostname to the etc/hosts.permit file. Past adding the following line, but the following IP would exist allowed to constitute an SSH connectedness with your remote server:
sshd : ten.x.0.5, LOCAL Go on in mind that such a limiting security setting can impact administering capabilities on your remote servers.
Cheque if fail2ban Banned Your IP Address
If you've tried to connect on multiple occasions, your IP might be blocked by an intrusion prevention software. Fail2ban is a service designed to protect you from brute force attacks, and it tin can misinterpret your authentication attempts as an attack.
Fail2ban monitors and dynamically alters firewall rules to ban IP addresses that exhibit suspicious beliefs. It monitors logs, similar the hosts.deny and hosts.allow files we edited previously.
In our example, nosotros used the post-obit control to check if the iptables tool is rejecting your attempted connections:
sudo iptables -L --line-number The output in your concluding window is going to list all hallmark attempts. If you notice that a firewall is indeed preventing your SSH connection, y'all can white-list your IP with fail2ban. Otherwise, the service is going to block all future attempts continuously. To access the fail2ban configuration file, enter the following command:
sudo nano /etc/fail2ban/jail.conf Edit the file past uncommenting the line that contains "ignoreip =" add the IP or IP range you lot want to white-list.
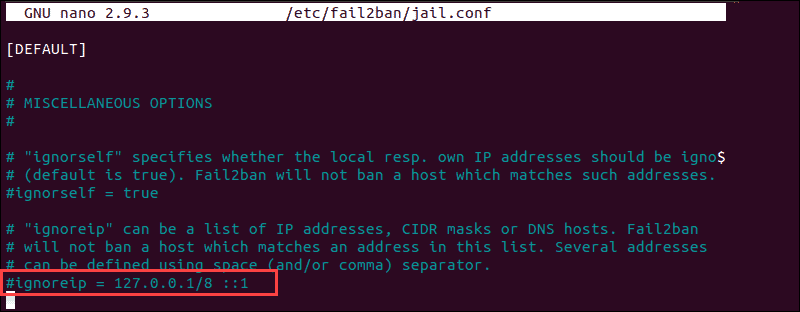
Fail2ban is now going to make an exception and not report suspicious beliefs for the IP in question.
Check the sshd_config File
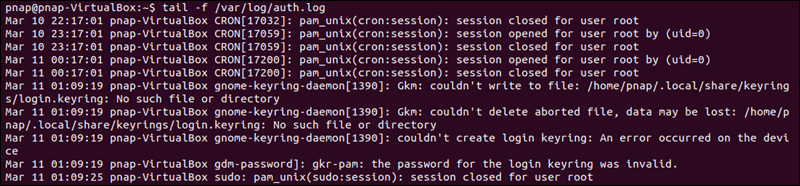
If you are continuing to experience the 'ssh_exchange_identification: read: Connectedness reset past peer' mistake, examine the hallmark log entry. By default, the SSH daemon sends logging information to the arrangement logs. Access the /var/log/auth.log file after your failed attempt to login. To review the latest log entries type:
tail -f /var/log/auth.log The output presents the results of your authentication attempts, information about your user business relationship, authentication key, or password.
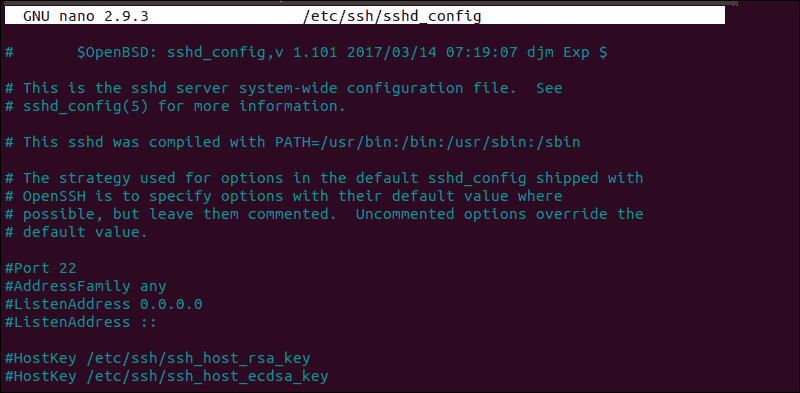
The log provides you with information that tin assist you find possible issues in the sshd configuration file, sshd_config. Any changes fabricated to the file can bear upon the terms nether which an ssh connection is established and atomic number 82 the remote server to care for the client every bit incompatible. To access the sshd_config file blazon:
sudo nano /etc/ssh/sshd_config The sshd configuration file enables you to change basic settings, such every bit the default TCP port or SSH cardinal pairs for authentication, as well as more than advanced functions such as port-forwarding.
For case, the MaxStartups variable defines how many connections a system accepts in a predefined period. If yous take a arrangement that makes a large number of connections in a brusk timeframe, it might exist necessary to increase the default values for this variable. Otherwise, the remote system might refuse additional attempted ssh connections.
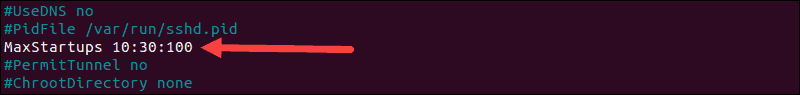
Anytime you edit the sshd_config file, restart the sshd service for the changes to take effect:
service sshd restart Only edit the variables that you are familiar with. A server can become unreachable as a result of a faulty configuration file.
Conclusion
Yous have thoroughly checked the most mutual reasons behind the "ssh_exchange_identification: read: Connection reset by peer" mistake. By looking at each possibility, in turn, you have successfully solved the issue and now know how to deal with similar bug going forward.
The number of potential causes is vast and difficult to troubleshoot in every respect. Ultimately, if the error persists, it might be necessary to contact your host.
Was this article helpful?
Aye No
Source: https://phoenixnap.com/kb/fix-connection-reset-by-peer-ssh-error
0 Response to "Couldn't Read Packet: Connection Reset by Peer"
Post a Comment